Does Cloud end the Data-center virtualization journey? We could see the buzz around cloud technologies from the past few years and Cloud service providers also keep posting great revenues. Amazon AWS and Microsoft Azure are leading cloud service providers in IaaS. Forrester predicts that along with Google cloud platform, these three companies will hold 76% […]
VMware vSphere 6.5 – Features – Quick Walk-through
VMware vSphere 6.5 – Features – Quick Walk-through. This article is intended to share some of the impressive features of VMware vSphere 6.5. VMware has worked on security areas, User interfaces , Containers and vCenter appliance on their lasted package “VMware vSphere 6.5” and it’s worth upgrading to that. You have to obtain new licenses to deploy […]
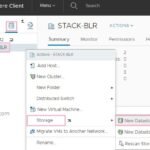
Creating Datastore – VMware vSphere 6.5 – Web-client
Create datastore on VMware vSphere 6.5 using the HTML based Web client. To store the virtual machines, you must have the storage repositories to configured. You can set up datastores on any SCSI-based storage devices that the host discovers, including Fibre Channel, iSCSI, and local storage devices. In this demonstration, we will choose one of the […]
VMware Products – Upgrade and Licensing Requirements
VMware Products – Upgrade and Licensing Requirements. You must keep upgrading to the new version of the existing VMware products that is used in your environment . Otherwise , VMware software might became absolute and upgrade may not be possible at one stage. Here , we will discuss more about VMware vSphere and other infrastructure […]
Oracle Solaris – Performance Troubleshooting using DTrace Toolkit
In this article, we will look at DTrace toolkit which is used to troubleshoot performance issues on Solaris operating systems. One of the co-authors of Solaris Performance and Tools [McDougall2007V2], Brendan Gregg, created this toolkit. It contains numerous d-scripts as well as Perl scripts that pre-process and post-process DTrace. DTrace toolkit is included in Oracle Solaris 11 and the […]
Create SSO Users using ssh – dir-cli – VCSA 6.5
Create SSO users using SSH session on VCSA 6.5 with help of dir-cli utility. I had faced the strange issue after VCSA 6.5 deployment on My LAB that SSO account was not created. Could be my mistake and haven’t followed the best practice for the VCSA 6.5 deployment. But I have figured out the way […]
Deploying Altaro VM Backup – Protect VMware & Hyper-V
Altaro VM Backup is affordable and easy to use backup solution for VMware vSphere and Hyper-V virtualization environments. Altaro VM Backup execute quickly and easily and it gives complete control over backup/restore jobs which is crucial. Altaro VM Backup provides you with quick access to all hosts in your environment. It supports multiple technologies like SQL, Exchange, consistent […]
How to fix Meltdown & Spectre Vulnerabilities on Redhat Linux?
Redhat is closely working with Intel and AMD to mitigate the risk of micro-architectural (hardware) implementation issues which are named as Meltdown and Spectre. These vulnerabilities are mostly affecting many modern microprocessors which include Intel, AMD, IBM power and ARM processors. These issues can be overcome by updating Linux kernel, virtualization-related components, and/or in combination with […]
Vulnerabilities – How to Fix Meltdown and Spectre on VMware vSphere ?
VMware vSphere also affected by multiple vulnerabilities since its uses Intel/AMD platforms. VMware vSphere has multiple layers of virtualization and sadly, you should apply/update the patches for all the components which includes Operating systems, virtual machines, virtual appliances, hypervisors, server firmware, and CPU microcode. Operating system patches can reduce the risk with help of hypervisor patches without […]
Meltdown and Spectre Vulnerabilities – Big Threats
Meltdown and Spectre Vulnerabilities have made 80% of servers as Vulnerable in overnight, thanks to Google Project Zero team and other security researchers who have brought such a worst vulnerabilities to the world (At least now). Meltdown vulnerability basically melts security boundaries which are normally enforced by the hardware (CPU). Spectre name is based on the root cause, “speculative […]